Spartacus Ransomware
Original Issue Date:-
May 02, 2018
Virus Type:-
Ransomware
Severity:-
High
It has been reported that new variants of ransomware named
The interesting part of this ransomware is that it does not try to communicate to any author or C2 server. The ransomware itself contain the RSA public key which it used to encrypt the AES key, generated at victim machine through which it encrypt all the files of the victim machines. As AES key were generated at the victim machine so there is slight chance for recovery of these keys using the process memory dump.
Once the ransomware reach at the victim computers, it check that only one instance of the ransomware would run on the victim machine. After this, ransomware search all the folders, files to encrypt and also generate the unique AES key. Finally the ransomware start encrypting all the files using AES key generated in previous step and add the .Spartacus or .[MastersRecovery@protonmail.com].Spartacus extension to all the encrypted files. After encrypting all the files, Spartacus will also delete the Shadow Volume Copies so that recovery cannot possible and drop a .txt file (as shown in figure1)which contains the message asking for ransom and RSA-encrypted AES key, which it ask the victim to send in email in order to decrypt its files.
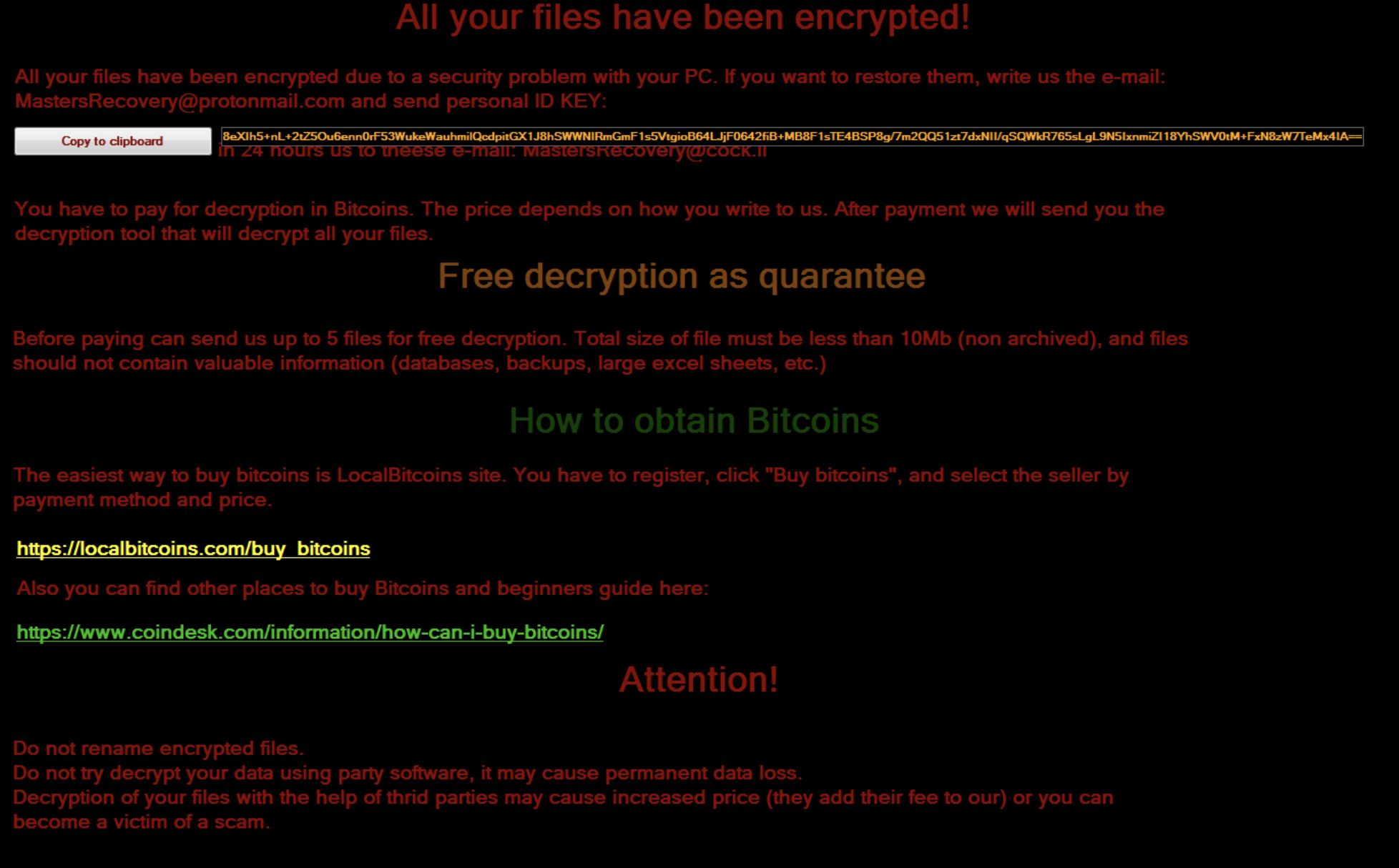
Fig1. Txt File (Source: Malware bytes)
Countermeasures and Best practices for prevention.
- Perform regular backups of all critical information to limit the impact of data or system loss and to help expedite the recovery process.Ideally, this data should be kept on a separate device, and backups should be stored offline.
- Restrict execution of powershell /WSCRIPT in enterprise environment Ensure installation and use of
the latest version (currently v5.0) of PowerShell, with enhanced logging enabled. script block
logging, and transcription enabled. Send the associated logs to a centralized log repository for
monitoring and analysis.
Reference:https://www.fireeye.com/blog/threat-research/2016/02/greater_visibilityt.html - Establish a Sender Policy Framework (SPF) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA% and %TEMP% paths.Ransomware sample drops and executes generally from these locations.
- Don't open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization’s website directly through browser
- Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
- Consider encrypting the confidential data as the ransomware generally targets common file types.
References


