Mamba ransomware
Original Issue Date:- August 18, 2017
Virus Type:- Ransomware
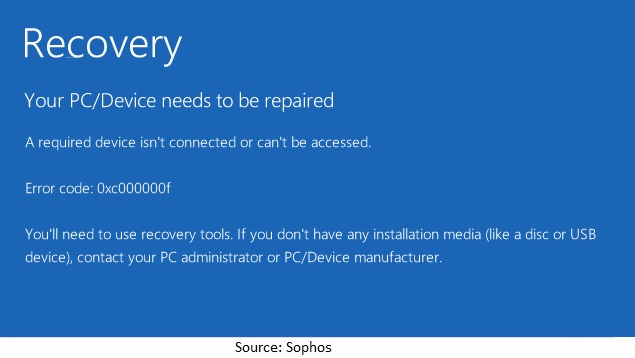
It has been reported that new variants of disk-encrypting ransomware named “Mamba” are spreading. The ransomware is also known as “HDDCryptor” because it encrypts the entire hard drives attached to the infected system. It also overwrites the Master Boot Record (MBR) with a modified bootloader. Once the system infected with mamba, it will boot to the screen shown below and ask to contact at email for decryption key.

Aliases:
Troj/Mamba, RANSOM_HDDCRYPTOR.AUSE, Ransom.HDDCryptor, Ransom.Mambretor.A5, Trojan-Ransom.Win32.Dcryptor, TR/FileCoder
Unlike other ransomware, Mamba shows no demands for money except the contact email id and the ID number. Mamba actors first gain access of organization network and then uses the PSEXEC utility to implant the Mamba executable.
Installations:
It is been reported that Mamba ransomware works in two stages. The initial stage is dropping “DiskCryptor” components on system, installs DiskCryptor driver, register system service (DefragmentService) and reboot affected machine.
In second stage, ransomware overwrites the Master Boot Record (MBR) with a modified bootloader and encrypt disk partitions using DiskCryptor software, clean up and finally reboot infected machine. The machine will boot up to the screen shown above and asks to contact on the displayed email ID and the key to decrypt.
Mamba service has the credentials to install DiskCryptor quietly in the background after rebooting. Mamba installs a regular copy of DiskCryptor, which can be find at directory C:\DC22 after the unexpected reboot.
Older operating system versions and older hard disks used a format called MBR (Master Boot Record). Modern OS installations use a similar-but-different disk layout called GUID Partition Table. After infection, most recent Windows systems may boot up to the screen shown below:
Indicators of compromise (IOC):
79ED93DF3BEC7CD95CE60E6EE35F46A1 (File Hash)
Mamba may create folder C:\xampp\http for dropping DiskCryptor installer files.
It installs “DiskCryptor” in directory “C:\DC22”
Many of the antivirus engines detect the ransomware Mamba binaries/executables.
Removal Tools:
Download Free Bot Removal Tool
Best practices and remedial measures:
- Perform regular backups of all critical information to limit the impact of data or system loss and to help expedite the recovery process. Ideally, this data should kept on a separate device, and backups should be stored offline.
- Check regularly for the integrity of the information stored in the databases.
- Regularly check the contents of backup files of databases for any unauthorized encrypted contents of data records or external elements, (backdoors /malicious scripts.)
- Ensure integrity of the codes /scripts being used in database, authentication and sensitive systems
- Establish a Sender Policy Framework (SPF) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Keep the operating system third party applications (MS office, browsers, browser Plugins) up-to-date with the latest patches.
- Application white listing/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA% and %TEMP% paths. Ransomware sample drops and executes generally from these locations.
- Maintain updated Antivirus software on all systems
- Don't open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization's website directly through browser
- Follow safe practices when browsing the web. Ensure the web browsers secured enough with appropriate content controls.
- Network segmentation and segregation into security zones - help protect sensitive information and critical services. Separate administrative network from business processes with physical controls and Virtual Local Area Networks.
- Disable ActiveX content in Microsoft Office applications such as Word, Excel, etc.
- Disable remote Desktop Connections, employ least-privileged accounts. Limit users who can log in using Remote Desktop, set an account lockout policy. Ensure proper RDP logging and configuration.
- Restrict access using firewalls and allow only to selected remote endpoints, VPN may also be used with dedicated pool for RDP access
- Use strong authentication protocol, such as Network Level Authentication (NLA) in Windows.
- Additional Security measures that may be considered are
- Use RDP Gateways for better management
- Change the listening port for Remote Desktop Tunnel Remote Desktop connections through IPSec or SSH Two-factor authentication may also be considered for highly critical systems
- If not required consider disabling, PowerShell / windows script hosting.
- Restrict users' abilities (permissions) to install and run unwanted software applications.
- Enable personal firewalls on workstations.
- Implement strict External Device (USB drive) usage policy.
- Employ data-at-rest and data-in-transit encryption.
- Consider installing Enhanced Mitigation Experience Toolkit, or similar host-level anti-exploitation tools.
- Block the attachments of following file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
- Individuals or organizations are not encouraged to pay the ransom, as this does not guarantee files will be released. Report such instances of fraud to CERT-In and Law Enforcement agencies.
References
- https://nakedsecurity.sophos.com/2016/09/27/mamba-ransomware-strikes-at-your-whole-disk-not-just-your-files/
- https://securelist.com/the-return-of-mamba-ransomware/79403/
- https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/disk-locking-hddcryptor-mamba-ransomware-makes-a-comeback
- https://www.sophos.com/en-us/medialibrary/Gated%20Assets/white%20papers/sophosransomwareprotectionwpna.pdf?la=en


