Autolycos Malware
Original Issue Date:-
July 22, 2022
Virus Type:-
Android Malware
Severity:-
High
It has been reported that a recently surfaced Android malware named ‘Autolycos Malware’ was hosted on Google Play Store and reportedly downloaded over 3,000,000 times. The malware belonging to the category of fleeceware has been discovered to be present in at least eight Android apps that subscribe users to premium services without their knowledge or consent by accessing users’ SMS messages.
These 8 infected applications have been removed from the Google Play Store, but those users who still have them installed on their devices are on the risk of being charged with costly subscription fees by the malware's activities.
- Vlog Star Video Editor (com.vlog.star.video.editor) – 1 million downloads
- Creative 3D Launcher (app.launcher.creative3d) – 1 million downloads
- Wow Beauty Camera (com.wowbeauty.camera) – 100,000 downloads
- Gif Emoji Keyboard (com.gif.emoji.keyboard) – 100,000 downloads
- Freeglow Camera 1.0.0 (com.glow.camera.open) – 5,000 downloads
- Coco Camera v1.1 (com.toomore.cool.camera) –1,000 downloads
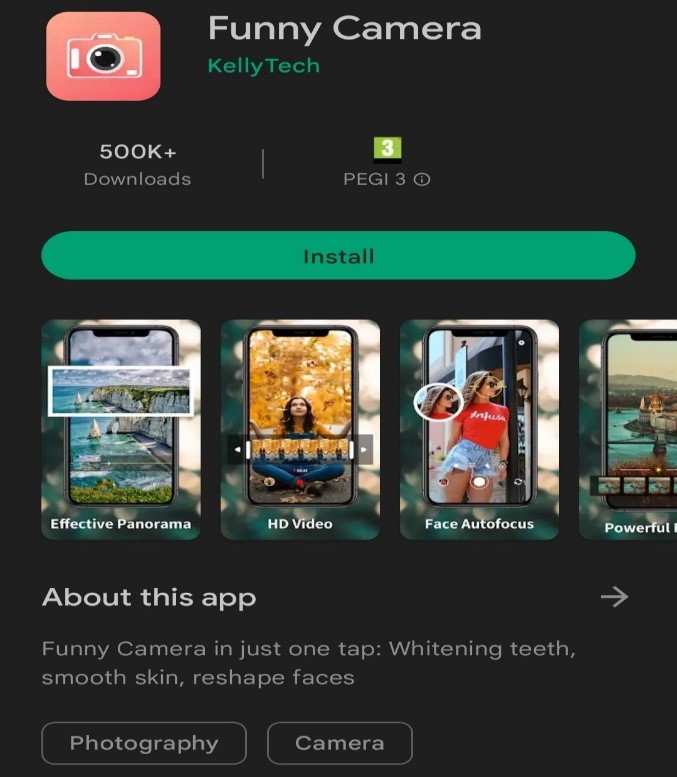
- 'Funny Camera' by KellyTech – 500,000 downloads
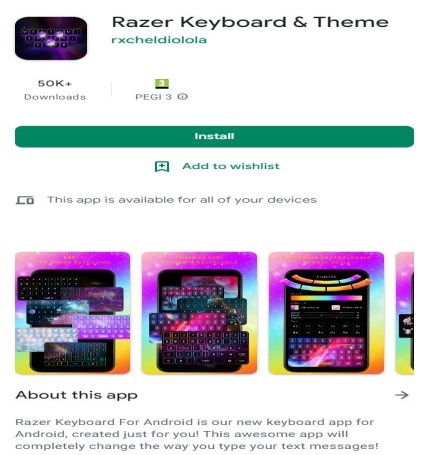
- Razer Keyboard & Theme' by rxcheldiolola - 50,000 downloads
Infection Mechanism:
Autolycos has been customized to evade detection by launching fraud attempts by executing http requests without using a browser. Instead of using webviews, Autolycos malware creates a remote browser and after execution of URLs on remote browser, it embeds the results in http request to make it harder for users to differentiate apps infected from Autolycos from the genuine apps as it is meant to make its actions less noticeable and thus not be detected by users of compromised devices.
To promote the apps to new users, the Autolycos operators had created numerous advertising campaigns on social media, which has resulted in making the infected apps popular to users and ultimately lead to numerous downloads. This has even enabled ranking up the infected apps high on the Google Play Store, which in turn increased their chances of getting downloaded by the smartphone users.
As the malware is capable to access the verification PIN code by reading the phone’s notifications, thus, the malicious applications has been successful in subscribing users to premium Direct Carrier Billing (DCB) services without informing users or taking their explicit consent.
IoC:
- Vlog Star Video Editor (com.vlog.star.video.editor)
- Creative 3D Launcher (app.launcher.creative3d)
- Wow Beauty Camera (com.wowbeauty.camera)
- Gif Emoji Keyboard (com.gif.emoji.keyboard)
- Freeglow Camera 1.0.0 (com.glow.camera.open)
- Coco Camera v1.1 (com.toomore.cool.camera)
- 'Funny Camera' by KellyTech
- Razer Keyboard & Theme' by rxcheldiolola
Countermeasures:
- Though these 8 infected apps has been deleted by Google from Play Store. However, if users have downloaded any of these apps, it is advisable that users shoulds delete them immediately.
- Verify app permissions and grant only those permissions which have relevant context for the app's purpose. It is also advisable that users don’t give permission to read SMS contents to apps and enable Google Play Protect on your Android devices.
- To stay safe against these threats, Android users should monitor background internet data and battery consumption.
- Use genuine mobile security solutions that can protect devices against online threats, malicious applications, and even data loss.
- Prior to downloading / installing apps on android devices (even from Google Play Store), Always review the app details, number of downloads, user reviews, comments and "ADDITIONAL INFORMATION" section.
- Install Android updates and patches as and when available from Android device vendors.
- Confirm that the banking/financial app you’re using is the official, verified version.
- If anything looks awry or suddenly unfamiliar, check in with your bank’s/financial service provider's customer service team.
- Use multi-factor authentication if it’s available Use biometric enabled authentication methods which provides a secure and uncrackable access control solution that doesn't expose your information to cybercriminals.
- Refer to security best practices for mobile Phone users: https://www.csk.gov.in/documents/Mobile_phone_Security.pdf
References:
- https://www.bleepingcomputer.com/news/security/new-android-malware-on-google-play-installed-3-million-times/
- https://threatpost.com/google-boots-malware-marketplace/180241/
- https://www.androidpolice.com/autolycos-android-malware-downloaded-three-million-times-play-store/
- https://www.bgr.in/news/this-android-malware-was-caught-stealing-money-from-play-store-apps-check-list-here-1298380/


