Akira Ransomware
Original Issue Date:-
July 25, 2023
Virus Type:- Ransomware
Severity:-
High
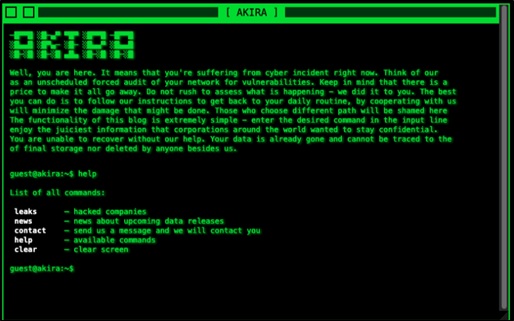
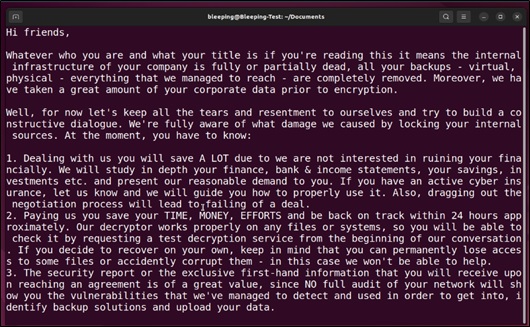
It has been reported that a recently emerged Ransomware operation dubbed Akira is active in cyberspace. This ransomware is targeting both Windows and Linux-based systems. This group first steals the information from the victims, then encrypt data on their systems and conducts double extortion to force the victim into paying the ransom. In case the victim does not pay, they release their victim's data on their dark web blog. The group is known to access victim environments via VPN services, particularly where users have not enabled multi-factor authentication. The group has also utilized tools such as AnyDesk, WinRAR, and PCHunter during intrusions. These tools are often found in the victim's environment, and their misuse typically goes unnoticed.
Infection Mechanism
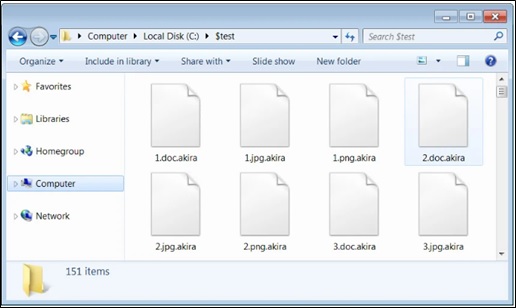
The attack process begins when a sample of the Akira ransomware is executed. Upon execution, Akira deletes the Windows Shadow Volume Copies on the targeted device. The ransomware then encrypts files with a predefined set of extensions. A '.akira' extension is appended to each encrypted file's name during this encryption process.
In the encryption phase, the ransomware terminates active Windows services using the Windows Restart Manager API. This step prevents any interference with the encryption process. It encrypts files found in various hard drive folders, excluding the ProgramData, Recycle Bin, Boot, System Volume Information, and Windows folders. To maintain system stability, it refrains from modifying Windows system files, which include files with extensions like .sys, .msi, .dll, .lnk, and .exe.
Attack Mapping: (MITRE ATT&CK Techniques)
- T1078 - Valid Accounts
- T1133 – External Remote Service
- T1059.001- PowerShell
- T1003.001 - OS Credential Dumping: LSASS Dumping
- T1112 - Modify Registry
- T1083- File and Directory Discovery
- T1486 -Data Encrypted for Impact
- T1490 - Inhibit System Recovery
Data Leak site:
https[://]akiral2iz6a7qgd3ayp3l6yub7xx2uep76idk3u2kollpj5z3z636bad[.]onion
Indicator of Compromise:
Hashes:
- 431d61e95586c03461552d134ca54d16
- af95fbcf9da33352655f3c2bab3397e2
- c7ae7f5becb7cf94aa107ddc1caf4b03
- d25890a2e967a17ff3dad8a70bfdd832
- e44eb48c7f72ffac5af3c7a37bf80587
- 1d3b5c650533d13c81e325972a912e3ff8776e36e18bca966dae50735f8ab296
- 302f76897e4e5c8c98a52a38c4c98443
- 9180ea8ba0cdfe0a769089977ed8396a68761b40
Best Practices and Recommendations:
- Ransomware infections primarily keep data as hostage. Therefore, it is recommended to maintain offline backups of critical data and ensure that these backups stay up to date to prevent data loss in the event of ransomware infection.
- All operating systems and applications should be kept updated regularly. Virtual patching can be considered for protecting legacy systems and networks. This measure hinders cybercriminals from gaining easy access to any system through vulnerabilities in outdated applications and software.
- Periodic Backups and restoration tests to check the restoration integrity.
- Establish Domain-based Message Authentication, Reporting, and Conformance (DMARC), Domain Keys Identified Mail (DKIM) and Sender Policy Framework (SPF) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Enforce strong password policies and multi-factor authentication (MFA).
- Avoid applying updates/patches available in any unofficial channel.
- Implement a strict External Device (USB drive) usage policy.
- Employ data-at-rest and data-in-transit encryption.
- Consider installing the Enhanced Mitigation Experience Toolkit or similar host-level anti-exploitation tools.
- Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
- Conduct vulnerability Assessment and Penetration Testing (VAPT) and information security audits of critical networks/systems, especially database servers, from CERT-IN empanelled auditors. Repeat audits at regular intervals.
- For detailed recommendations, please refer to "Best Practices and Remedial Measures" at https://www.csk.gov.in/alerts/ransomware.html
References:
- https://www.bleepingcomputer.com/news/security/meet-akira-a-new-ransomware-operation-targeting-the-enterprise
- https://news.sophos.com/en-us/2023/05/09/akira-ransomware-is-bringin-88-back
- https://blog.pulsedive.com/akira-ransomware
- https://www.cert-in.org.in/PDF/RANSOMWARE_Report_2022.pdf
- https://www.csk.gov.in/alerts/ransomware.html


